Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right tool.
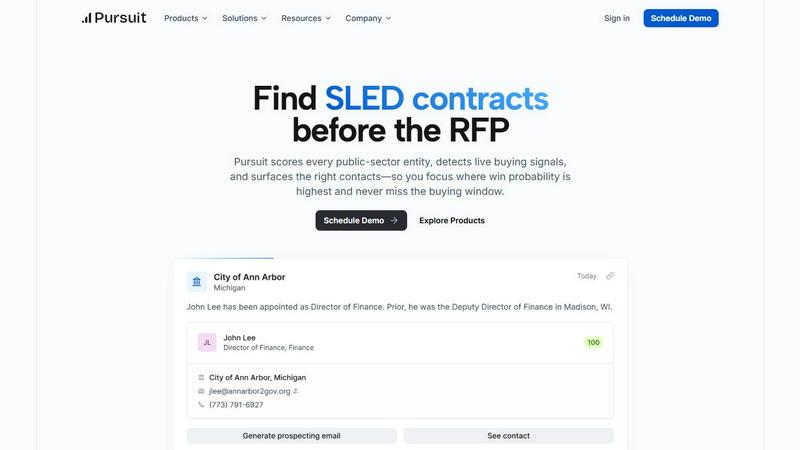
Pursuit
Pursuit uses AI to find you the best public sector sales opportunities before anyone else.
Last updated: February 28, 2026
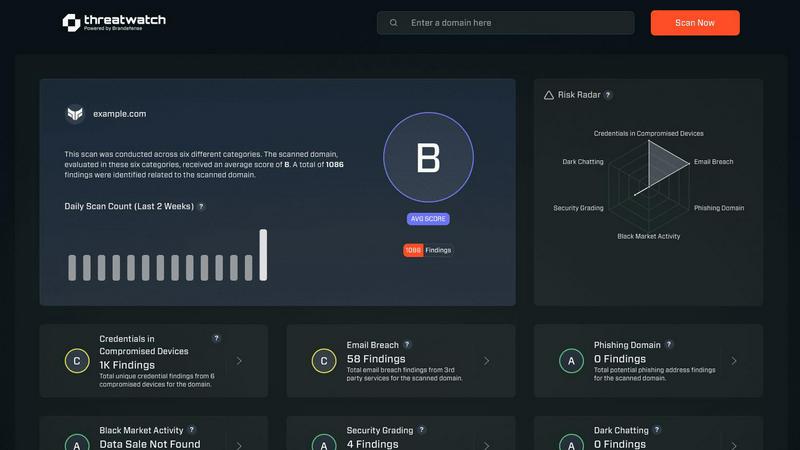
Threat Watch
Quickly assess your cybersecurity health and get easy steps to enhance your protection against online threats.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Buying Signal Detection
Pursuit's AI continuously scans and analyzes public records to detect genuine buying signals 6 to 18 months before an RFP is officially published. This includes monitoring for budget approvals, discussions in council meetings, contract expirations, and new strategic initiatives. By alerting you this early, you can engage with prospects while their needs are being formed, positioning your solution as the obvious choice long before competitors even know the opportunity exists.
Entity Scoring & Prioritization
Instead of guessing which agencies to target, Pursuit scores every SLED entity based on live buying signals and your specific solution fit. This creates a daily prioritized list of accounts that are most likely to purchase. Your team can focus their energy on high-probability opportunities, dramatically improving efficiency and ensuring no critical budget window or leadership change is missed.
Automated Contact & Account Enrichment
Pursuit maintains a highly accurate and constantly updated database of contacts and organizational charts across the SLED market. It automatically enriches your target accounts with the right decision-makers, their roles, and contact information. This eliminates manual research, ensures your data is fresh, and helps you build accurate outreach lists instantly.
Native CRM & Tool Integrations
Pursuit seamlessly connects with your existing sales stack to ensure intelligence flows directly into your workflow. With native, bi-directional sync for Salesforce and HubSpot, all enriched account data, buying signals, and contact updates are automatically pushed to your CRM. This means no manual data entry is required, and your entire team operates from a single source of truth.
Threat Watch
Continuous Scanning
Threat Watch continuously scans your digital landscape to identify vulnerabilities and potential threats in real-time. This proactive approach ensures that you are always aware of your cybersecurity posture, allowing you to take immediate action when necessary.
Compromised Credentials Monitoring
With Threat Watch, you can monitor for compromised credentials across various platforms. If any of your accounts are found to have leaked passwords, you will be alerted promptly, enabling you to take swift action to secure your accounts.
Dark Web Monitoring
Threat Watch dives deep into the dark web to uncover any mentions or data leaks related to your organization. This feature helps you stay one step ahead of cybercriminals by identifying potential threats before they escalate.
Guided Risk Remediation
Not only does Threat Watch identify risks, but it also provides guided steps to resolve them. This feature is particularly useful for teams without dedicated security experts, offering clear instructions on how to enhance your cybersecurity measures effectively.
Use Cases
Pursuit
For BDRs: Daily Prioritized Outreach
Business Development Representatives can stop cold calling blindly. Pursuit provides daily, tailored call and email lists based on the hottest buying signals in their territory, such as recent budget approvals or contract expirations. This allows BDRs to have relevant, timely conversations that significantly increase conversion rates and build a more qualified pipeline.
For Account Executives: Instant Meeting Preparation
Account Executives can walk into every call fully prepared. With the Pursuit Chrome extension, they can pull up a complete dossier on any agency directly from their browser, seeing the incumbent vendor, contract history, recent buying signals, and key contacts. This deep preparation builds credibility and directly contributes to higher win rates.
For Marketing: Signal-Driven ABM Campaigns
Marketing teams can build highly effective Account-Based Marketing (ABM) campaigns grounded in real intelligence. By targeting lists of accounts showing specific buying intent—like a new technology initiative in a city's budget—campaigns become more relevant. Pursuit can sync these high-intent audiences directly to platforms like LinkedIn Ads, HubSpot, or Marketo.
For Customer Success: Proactive Renewal Management
Customer Success managers can protect and grow revenue by getting early alerts for renewal opportunities and churn risks. Pursuit notifies them 90-180 days before a contract expires and monitors for signals like budget cuts or competitor activity at their accounts. This allows for proactive conversations to secure renewals faster and mitigate risk.
Threat Watch
Business Owner Protection
As a business owner, protecting your digital assets is crucial. Threat Watch allows you to monitor online mentions of your business, compromised credentials, and potential vulnerabilities, ensuring your company's reputation and data remain secure.
IT Team Support
IT teams can leverage Threat Watch to gain insights into the security status of their organization. By utilizing its automated assessments, IT professionals can focus on managing other critical tasks while being alerted to any emerging security risks.
Security Team Efficiency
Security teams can enhance their efficiency with Threat Watch's comprehensive scanning and reporting capabilities. This tool helps teams prioritize their efforts by providing a clear picture of the most significant threats to address first.
Compliance Assurance
Organizations that need to comply with industry regulations can use Threat Watch to demonstrate their commitment to cybersecurity. By continuously monitoring and addressing vulnerabilities, businesses can maintain compliance and avoid potential penalties.
Overview
About Pursuit
Pursuit is your dedicated AI-powered guide to navigating the complex world of state, local, and education (SLED) government sales. If you've ever felt overwhelmed by the scale, slow timelines, and hidden processes of public sector procurement, Pursuit is designed to change that experience entirely. It acts as an all-in-one sales intelligence platform that transforms confusion into clarity and dead ends into actionable opportunities. Built for sales teams, business development reps, and operations professionals at companies selling to the government, Pursuit's core mission is to remove friction. It does this by continuously analyzing a massive amount of public data—like budget documents, meeting minutes, and procurement postings—to surface real-time buying signals long before a formal Request for Proposal (RFP) is released. This means you can identify which of the 110,000+ SLED entities are actively planning to buy, understand their specific needs, and reach the right contacts at the perfect time. With Pursuit, you gain enterprise-level research for every target, allowing your team to spend less time searching in the dark and more time building the relationships that win valuable contracts.
About Threat Watch
Threat Watch is your comprehensive cybersecurity health dashboard, crafted to provide clear insights and control over your organization's digital safety. In an era where online threats proliferate from various sources—such as leaked passwords, unpatched software, and even mentions on the dark web—having a robust defense is essential. Threat Watch makes safeguarding your organization easier by continuously scanning and analyzing your digital assets, vulnerabilities, and exposures across the internet. This tool is tailored for business owners, IT managers, and security teams who may lack dedicated cybersecurity expertise. Its primary value lies in offering real-time insights and automated assessments, empowering you to shift from feeling overwhelmed to being proactive. With Threat Watch, you can swiftly identify your most pressing risks, understand their implications, and receive guided steps to mitigate them, all from a single, user-friendly platform. Think of it as a regular check-up for your company's online health, helping you prevent security breaches before they occur.
Frequently Asked Questions
Pursuit FAQ
What makes SLED sales different from other markets?
Selling to state, local, and education governments involves a massive scale of over 110,000 unique entities, each with its own procurement rules and annual budget cycles. Buying decisions are public but the critical signals are buried in lengthy documents and meetings. Timing is everything, as missing a budget cycle can mean waiting an entire fiscal year for the next chance.
How does Pursuit find buying signals so early?
Pursuit uses artificial intelligence to continuously scan and analyze millions of public data sources that indicate purchase intent. This includes budget documents, meeting agendas and transcripts, contract registries, and RFP postings. The AI is trained to identify key phrases and discussions related to planning, budgeting, and problem-solving that precede a formal procurement.
Can Pursuit integrate with our current CRM?
Yes, absolutely. Pursuit offers native, bi-directional integrations with major CRMs like Salesforce and HubSpot. This means enriched account and contact data, along with buying signals, automatically sync to your existing records. No engineering work is required, ensuring your team has the latest intelligence directly in their daily workflow.
Who on my team should use Pursuit?
Pursuit is built for the entire go-to-market team. Sales Leaders use it for forecasting and coverage analysis, Revenue Operations for data management, Marketing for ABM, Account Executives for deal insight, BDRs for targeted outreach, and Customer Success for renewal management. It provides specific value for every role involved in SLED revenue.
Threat Watch FAQ
What types of threats does Threat Watch monitor?
Threat Watch monitors a variety of threats, including compromised credentials, phishing addresses, breached accounts, and dark web content related to your organization.
How does Threat Watch help non-expert users?
Threat Watch is designed with user-friendliness in mind. It provides clear insights and guided steps for remediation, making it accessible even for users without extensive cybersecurity knowledge.
Can Threat Watch integrate with other security tools?
Threat Watch is designed to complement existing security measures and can be integrated with other tools to create a more robust cybersecurity posture for your organization.
Is there a free trial available for Threat Watch?
Yes, Threat Watch offers a free scan to help you uncover your cybersecurity health. This allows you to experience the benefits before committing to a subscription.
Alternatives
Pursuit Alternatives
Pursuit is an AI-powered sales intelligence platform built for businesses that sell to state, local, and education (SLED) government agencies. It falls into the business intelligence category, specifically designed to find and alert you to the best public sector sales opportunities before they become widely known. Even with a great tool like Pursuit, it's common to explore other options. You might be looking for a different pricing model, need a platform that covers different markets like federal government, or require specific integrations with your existing sales software. It's a smart step to ensure you find the perfect fit for your team's unique needs and budget. When evaluating alternatives, focus on what matters most for public sector sales. Look for platforms that offer real-time opportunity alerts, accurate contact data for government decision-makers, and insights into agency budgets and buying signals. The goal is to find a solution that saves you research time and helps you build relationships that lead to winning contracts.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity health dashboard that helps organizations monitor and improve their digital safety. As a tool designed for business owners, IT managers, and security teams, it simplifies the complex landscape of cybersecurity by providing real-time insights and automated assessments of an organization's security posture. Users often seek alternatives to Threat Watch for reasons such as pricing, specific feature sets, or compatibility with existing platforms. When considering alternatives, look for tools that offer a clear overview of your cybersecurity health, real-time monitoring capabilities, and easy-to-understand metrics. Additionally, ensure that the alternative you choose aligns with your organization's specific needs, whether that's budget constraints or specific security focus areas. Finding the right fit can help you maintain control over your cybersecurity without feeling overwhelmed.
