CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right tool.
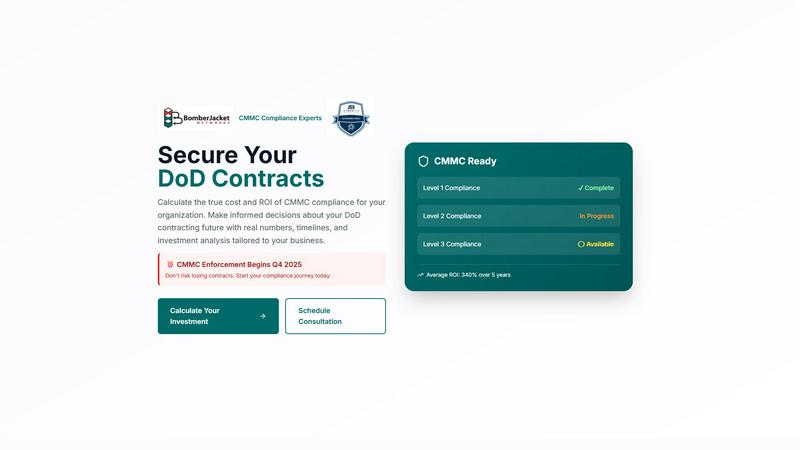
CMMC ROI
Easily calculate CMMC compliance costs and ROI to secure your DoD contracts and make informed investment decisions.
Last updated: March 1, 2026
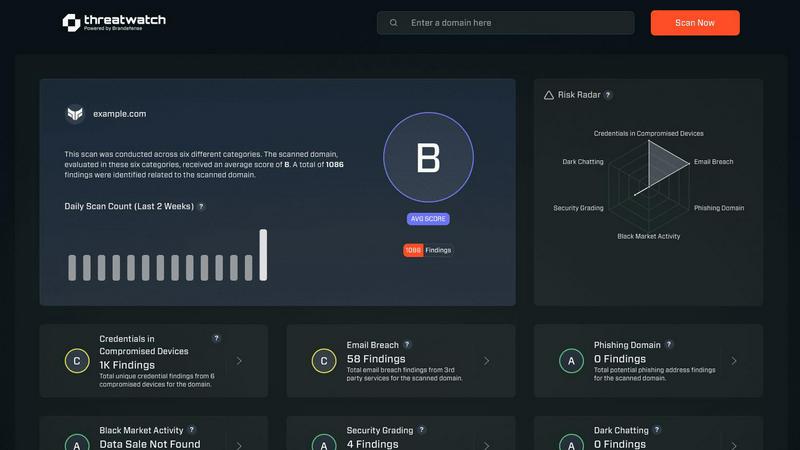
Threat Watch
Quickly assess your cybersecurity health and get easy steps to enhance your protection against online threats.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Comprehensive Financial Analysis
CMMC ROI offers a complete financial analysis of CMMC compliance by evaluating costs, potential savings, and revenue protection. Users can see how compliance impacts their bottom line and understand the return on investment they can expect.
Personalized Cost Estimates
The tool allows users to input their specific company size, annual DoD revenue, and required CMMC level to receive tailored investment estimates. This feature ensures that the financial analysis reflects the unique circumstances of each contractor.
ROI Calculation and Visualization
CMMC ROI provides an easy-to-understand calculation of ROI, factoring in protected revenue and implementation costs. Users can visualize their investment timeline, including break-even points and potential returns over a five-year period.
Progress Tracking and Consultation
With features that enable users to track their compliance progress and seek expert consultation, CMMC ROI supports contractors throughout their compliance journey. Users can schedule consultations to receive personalized advice and strategic insights into their compliance efforts.
Threat Watch
Continuous Scanning
Threat Watch continuously scans your digital landscape to identify vulnerabilities and potential threats in real-time. This proactive approach ensures that you are always aware of your cybersecurity posture, allowing you to take immediate action when necessary.
Compromised Credentials Monitoring
With Threat Watch, you can monitor for compromised credentials across various platforms. If any of your accounts are found to have leaked passwords, you will be alerted promptly, enabling you to take swift action to secure your accounts.
Dark Web Monitoring
Threat Watch dives deep into the dark web to uncover any mentions or data leaks related to your organization. This feature helps you stay one step ahead of cybercriminals by identifying potential threats before they escalate.
Guided Risk Remediation
Not only does Threat Watch identify risks, but it also provides guided steps to resolve them. This feature is particularly useful for teams without dedicated security experts, offering clear instructions on how to enhance your cybersecurity measures effectively.
Use Cases
CMMC ROI
Small Business Compliance Planning
A small contractor with limited resources can use CMMC ROI to evaluate the financial implications of achieving compliance. By entering their specific data, they can uncover potential ROI and make informed budgeting decisions.
Large Contractor Financial Strategy
A large prime contractor can utilize CMMC ROI to assess the financial impact of compliance at scale. By analyzing their substantial DoD contract revenue, they can strategize investment in cybersecurity measures and compliance processes effectively.
Risk Mitigation for FCI Contractors
FCI contractors can leverage CMMC ROI to identify the financial risks associated with non-compliance. This tool helps them recognize the importance of certification and avoid potential losses from contract cancellations.
ROI Benchmarking for Technology Firms
Technology firms working with DoD contracts can use CMMC ROI to benchmark their compliance costs against industry standards. This insight allows them to optimize their investments and enhance their competitive edge over non-certified competitors.
Threat Watch
Business Owner Protection
As a business owner, protecting your digital assets is crucial. Threat Watch allows you to monitor online mentions of your business, compromised credentials, and potential vulnerabilities, ensuring your company's reputation and data remain secure.
IT Team Support
IT teams can leverage Threat Watch to gain insights into the security status of their organization. By utilizing its automated assessments, IT professionals can focus on managing other critical tasks while being alerted to any emerging security risks.
Security Team Efficiency
Security teams can enhance their efficiency with Threat Watch's comprehensive scanning and reporting capabilities. This tool helps teams prioritize their efforts by providing a clear picture of the most significant threats to address first.
Compliance Assurance
Organizations that need to comply with industry regulations can use Threat Watch to demonstrate their commitment to cybersecurity. By continuously monitoring and addressing vulnerabilities, businesses can maintain compliance and avoid potential penalties.
Overview
About CMMC ROI
CMMC ROI is an innovative, user-friendly investment calculator designed specifically for contractors working with the Department of Defense (DoD). This essential tool helps demystify the often complex financial aspects of CMMC compliance, which is crucial for safeguarding your business's future in government contracting. With CMMC enforcement set to commence in Q4 2025, contractors risk losing 100% of their DoD contract revenue without certification. CMMC ROI provides a personalized, data-driven analysis that enables businesses to understand the true costs of compliance and the potential return on investment (ROI). By translating intricate cybersecurity requirements into straightforward financial terms, it empowers both small businesses and large prime contractors to make informed decisions regarding their compliance journey, ensuring they are equipped with real numbers tailored to their specific size, revenue, and required certification levels.
About Threat Watch
Threat Watch is your comprehensive cybersecurity health dashboard, crafted to provide clear insights and control over your organization's digital safety. In an era where online threats proliferate from various sources—such as leaked passwords, unpatched software, and even mentions on the dark web—having a robust defense is essential. Threat Watch makes safeguarding your organization easier by continuously scanning and analyzing your digital assets, vulnerabilities, and exposures across the internet. This tool is tailored for business owners, IT managers, and security teams who may lack dedicated cybersecurity expertise. Its primary value lies in offering real-time insights and automated assessments, empowering you to shift from feeling overwhelmed to being proactive. With Threat Watch, you can swiftly identify your most pressing risks, understand their implications, and receive guided steps to mitigate them, all from a single, user-friendly platform. Think of it as a regular check-up for your company's online health, helping you prevent security breaches before they occur.
Frequently Asked Questions
CMMC ROI FAQ
What is CMMC ROI and how does it work?
CMMC ROI is a free investment calculator that helps DoD contractors assess the financial aspects of CMMC compliance. By inputting specific business details, users receive personalized insights into costs, ROI, and the value of maintaining compliance.
Why is CMMC compliance important for DoD contractors?
CMMC compliance is essential for DoD contractors as it ensures the protection of sensitive information and maintains eligibility for government contracts. Non-compliance risks losing significant revenue and market opportunities.
How does CMMC ROI calculate ROI?
CMMC ROI calculates ROI by assessing the protected revenue from DoD contracts, the costs of compliance implementation, and any breach cost avoidance. The formula is ROI = (Protected Value - Investment) / Investment × 100.
Can CMMC ROI be used by businesses of all sizes?
Yes, CMMC ROI is designed to cater to businesses of all sizes, from small contractors to large prime contractors. The tool provides tailored results based on specific company size, revenue, and required CMMC levels, making it accessible to everyone in the DoD contracting space.
Threat Watch FAQ
What types of threats does Threat Watch monitor?
Threat Watch monitors a variety of threats, including compromised credentials, phishing addresses, breached accounts, and dark web content related to your organization.
How does Threat Watch help non-expert users?
Threat Watch is designed with user-friendliness in mind. It provides clear insights and guided steps for remediation, making it accessible even for users without extensive cybersecurity knowledge.
Can Threat Watch integrate with other security tools?
Threat Watch is designed to complement existing security measures and can be integrated with other tools to create a more robust cybersecurity posture for your organization.
Is there a free trial available for Threat Watch?
Yes, Threat Watch offers a free scan to help you uncover your cybersecurity health. This allows you to experience the benefits before committing to a subscription.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a specialized investment calculator designed to assist Department of Defense contractors in understanding their compliance costs and potential returns on investment related to the Cybersecurity Maturity Model Certification (CMMC). As compliance becomes mandatory, many users seek alternatives due to various factors including pricing, feature sets, or specific platform requirements that might better align with their business needs. When exploring alternatives, it’s essential to consider the tool’s user-friendliness, how well it addresses your unique compliance challenges, and the level of customization it offers to ensure it meets your specific organizational goals.
Threat Watch Alternatives
Threat Watch is a comprehensive cybersecurity health dashboard that helps organizations monitor and improve their digital safety. As a tool designed for business owners, IT managers, and security teams, it simplifies the complex landscape of cybersecurity by providing real-time insights and automated assessments of an organization's security posture. Users often seek alternatives to Threat Watch for reasons such as pricing, specific feature sets, or compatibility with existing platforms. When considering alternatives, look for tools that offer a clear overview of your cybersecurity health, real-time monitoring capabilities, and easy-to-understand metrics. Additionally, ensure that the alternative you choose aligns with your organization's specific needs, whether that's budget constraints or specific security focus areas. Finding the right fit can help you maintain control over your cybersecurity without feeling overwhelmed.
