Phishly vs RocketShare
Side-by-side comparison to help you choose the right tool.
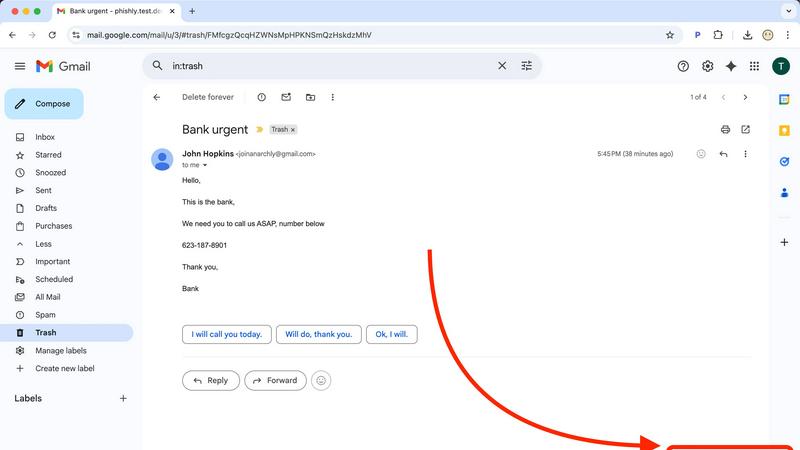
Phishly
Phishly helps you detect phishing emails effortlessly with AI-powered scanning in your browser and Gmail.
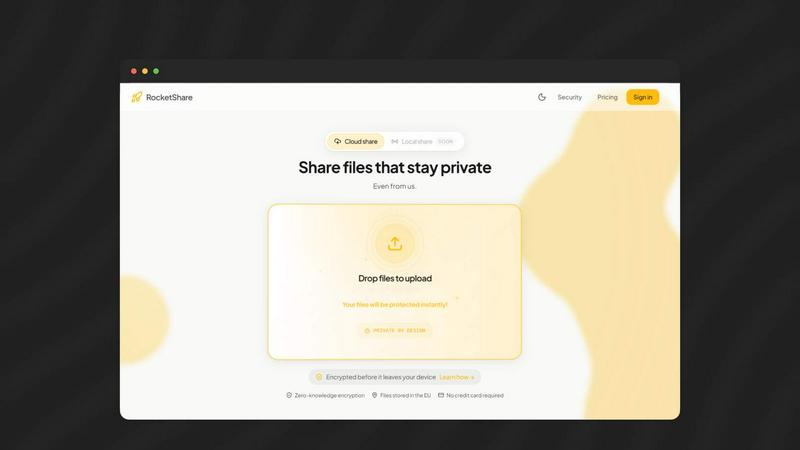
RocketShare
Share your files with total privacy using encryption we can't even access.
Last updated: March 4, 2026
Visual Comparison
Phishly
RocketShare
Feature Comparison
Phishly
AI-Powered Analysis
Phishly utilizes cutting-edge artificial intelligence to analyze emails for phishing threats. It evaluates multiple indicators such as domain authenticity and language urgency to provide reliable insights about potential risks.
Risk Assessment Categories
When Phishly scans an email, it categorizes the risk level as Safe, Medium Risk, or High Risk. This clear classification helps users quickly understand the threat level and decide how to proceed with the email in question.
User-Friendly Interface
With an intuitive design, Phishly is easy to use, even for those without technical expertise. The Chrome extension integrates seamlessly with Gmail, allowing users to scan emails with a single click, making email security accessible to everyone.
Privacy Protection
Phishly is committed to protecting user privacy. It only analyzes emails that you specifically choose to scan, ensuring that your personal data and email content remain confidential and secure from unwanted scrutiny.
RocketShare
Zero-Knowledge Encryption
This is the cornerstone of RocketShare's security. Your files are encrypted on your own computer or phone before they are uploaded. The encryption key never leaves your possession, meaning RocketShare's servers only receive and store data that is completely unreadable to them or anyone else. This guarantees that your privacy is absolute, as even the platform itself has "zero knowledge" of your file contents.
Client-Side Encryption
Building on the zero-knowledge model, client-side encryption means the entire encryption process happens locally on your device. You don't have to trust the security of an online server because the file is already locked and protected before it ever touches the internet. This gives you full control and peace of mind from the very first step.
Flexible Sharing Modes
RocketShare offers two main ways to send files to fit different needs. Use "Cloud Share" for convenient, asynchronous sharing where files are stored encrypted on secure EU-based servers for the recipient to download. Or, choose "Local Share" for a fast, peer-to-peer transfer that sends files directly between devices without them being stored online, perfect for very large files or when you need maximum speed.
EU-Based Data Storage
For users concerned with data sovereignty and regulations like GDPR, RocketShare stores all cloud-shared file data on servers located within the European Union. This provides an additional layer of legal and privacy assurance, ensuring your data is housed under some of the world's strictest data protection frameworks.
Use Cases
Phishly
Individual Email Security
For everyday users, Phishly offers peace of mind by allowing them to scan suspicious emails before clicking on links or downloading attachments. This simple step can prevent falling victim to phishing scams.
Small Business Protection
Small businesses often lack extensive IT resources. Phishly provides a straightforward solution for these businesses to protect their employees from phishing attacks, enhancing overall security without needing complex systems.
Educational Institutions
Teachers and students can use Phishly to verify the legitimacy of emails received from unknown senders. This is crucial in protecting sensitive information and maintaining a safe digital environment in educational settings.
Remote Workers Safety
As remote work becomes increasingly common, Phishly is an essential tool for remote employees. It helps them identify phishing attempts in their emails, safeguarding their personal and corporate data while working from home.
RocketShare
Legal Professionals and Law Firms
Lawyers can securely share sensitive case files, client contracts, and legal briefs with absolute confidentiality. RocketShare's zero-knowledge encryption ensures attorney-client privilege is technically enforced, as no third party can intercept or access the documents, providing a secure channel for critical communications.
Creative Professionals (Photographers/Videographers)
Photographers and videographers can deliver high-resolution client galleries or raw video footage without fear of unauthorized access or piracy. The platform allows them to send huge files easily while guaranteeing that their creative intellectual property is protected end-to-end, building trust with their clients.
Healthcare and Medical Practices
Healthcare providers can use RocketShare to exchange sensitive patient records, lab results, or medical imaging in a compliant manner. The strong encryption helps meet privacy standards by ensuring patient data is inaccessible during transfer and storage, safeguarding personal health information.
Business Teams and Accountants
Teams working on confidential projects, financial reports, or business strategies can collaborate safely. Accountants can share tax documents and financial statements with clients, knowing the data is encrypted before it leaves their computer, preventing any potential data breaches or leaks.
Overview
About Phishly
Phishly is an innovative AI-powered phishing detection platform designed to enhance your email security effortlessly. Available as a convenient Chrome extension for Gmail and a user-friendly web tool, Phishly allows users to scan emails with ease. Simply open any email in Gmail and click "Scan with Phishly," or paste suspicious emails directly on our website for instant analysis. Our advanced AI technology identifies various phishing indicators, including suspicious domains, urgent language, spoofed senders, and social engineering tactics. The platform provides clear risk assessments to help users understand the threat level of potential phishing attempts, categorized as Safe, Medium Risk, or High Risk, along with detailed explanations. Phishly is perfect for individuals and small businesses seeking straightforward phishing protection without the complexity often associated with enterprise solutions. We prioritize user privacy by analyzing only the emails you choose to scan, ensuring your data remains secure. With no technical knowledge required, Phishly is free to use and delivers instant answers when you need to verify the legitimacy of an email.
About RocketShare
RocketShare is a secure file-sharing platform built for anyone who values their privacy. It's designed to let you send files of any size with complete confidence, knowing that your data is protected from the moment you upload it. The core promise is simple: no one, not even the team at RocketShare, can ever access the content of your files. This is achieved through a powerful technology called zero-knowledge encryption. Here's how it works: your files are encrypted directly on your own device before they are ever sent over the internet. The key to unlock them stays with you, often built right into the shareable link you send. This means RocketShare's servers only ever handle scrambled, unreadable data. It offers enterprise-grade security in a beautifully simple, self-serve package that anyone can use. Whether you're a freelancer, a creative professional, or part of a large business team, RocketShare ensures your sensitive documents, client work, and intellectual property remain truly private. With options to share via the cloud or through a fast local connection, and with all data stored securely within the European Union, RocketShare is the perfect tool for combining top-tier security with effortless simplicity.
Frequently Asked Questions
Phishly FAQ
How does Phishly work?
Phishly analyzes emails using AI technology to detect phishing indicators. By assessing aspects like sender authenticity and the language used, it provides a risk assessment to help users understand potential threats.
Is Phishly free to use?
Yes, Phishly is completely free to use. There are no hidden fees or subscriptions, making it accessible for everyone, from individuals to small businesses looking for effective phishing protection.
Do I need technical skills to use Phishly?
No, Phishly is designed to be user-friendly for individuals without technical skills. Its intuitive interface allows anyone to scan emails easily and receive instant feedback on their safety.
How does Phishly protect my privacy?
Phishly only analyzes the emails that you explicitly choose to scan. This ensures that your personal data and email content remain private and secure, with no unauthorized access to your information.
RocketShare FAQ
How does RocketShare's encryption work?
RocketShare uses a method called zero-knowledge, client-side encryption. When you select a file to share, our application on your device immediately encrypts it using a unique key before it is uploaded. This key is what decrypts the file, and it is never sent to our servers. Often, this key is embedded in the download link you share. This means we only handle encrypted data that we cannot read or access.
What is the difference between Cloud Share and Local Share?
Cloud Share uploads your encrypted file to our secure servers in the EU, generating a link you can send. The recipient can download it anytime. Local Share creates a direct, peer-to-peer connection between your device and the recipient's device for the transfer. The file never passes through our servers, making it faster for large files and keeping it entirely off the cloud.
Is RocketShare really free to use?
Yes, you can start using RocketShare's core secure sharing features without providing a credit card. This allows you to experience the privacy and simplicity of the platform firsthand. We believe in making true security accessible to everyone from the start.
Where are my files stored?
For files shared via Cloud Share, the encrypted data is stored on our secure servers located within the European Union. For Local Share transfers, files are sent directly between devices and are not stored on any server. In both cases, the actual content of your files remains encrypted and inaccessible to anyone without the unique key.